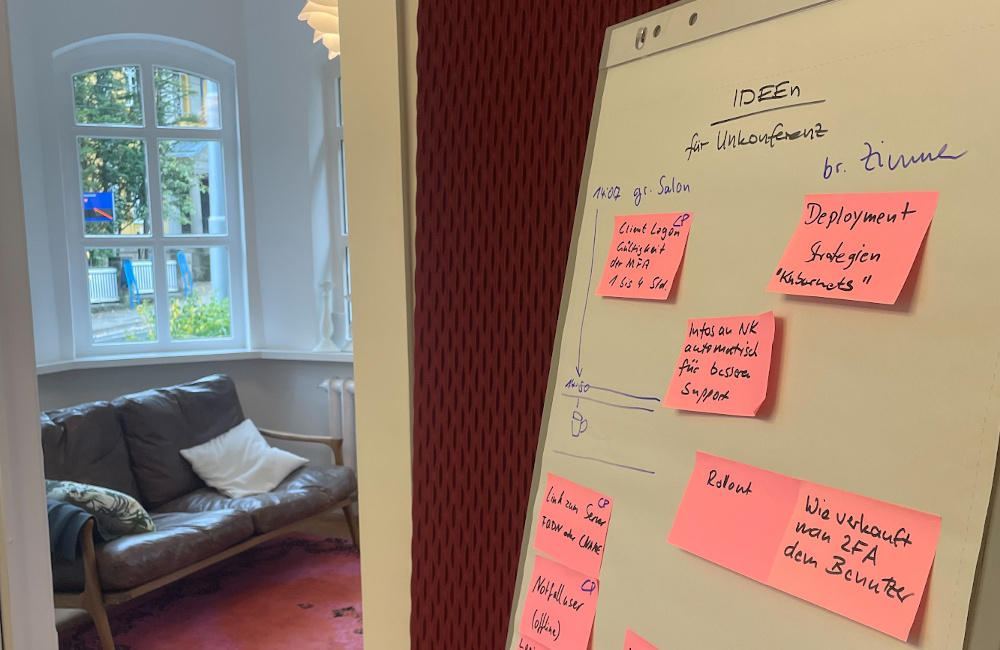
Third unconference by NetKnights

Take a break from everyday business life: NetKnights is holding its third internal unconference in the countryside of Saxony-Anhalt. During these days, the team consciously takes time to talk about important content and organizational matters. In this slowed-down contrast to everyday business life, the focus is also on working together as a team.
YubiHSM meets privacyIDEA

Multi-factor authentication also means trust. privacyIDEA offers several ways to store sensitive token data in an encrypted, secure manner, creating a strong trust anchor.
2FA customer workshop in Kassel
NetKnights GmbH held a customer workshop in Kassel. The new privacyIDEA version 3.8 was presented to the customers and the new features were discussed. The workshop was also a good opportunity to give our customers an insight into our daily work.
First Internal Hackathon at NetKnights

In retreat from the daily work routine, four NetKnights developers concentrated on the work on the future release 3.8 of the privacyIDEA server.
Definition of groups for querying the second factor and forwarding the HTTP headers
IT security company NetKnights releases version 1.1.0 of the privacyIDEA Keycloak plugin. In this version, groups can be created in which it is defined who should be queried for the second factor. In this version, groups can be created in which it is defined who should be queried for the second factor.
NetKnights in search of new colleagues

Once a year, the Department of Electrical Engineering and Computer Science at the University of Kassel organizes a company fair. NetKnights used this opportunity to exchange ideas with interested students.
New user interface and simplified configuration of push tokens

IT security company NetKnights releases version 4.0 of its privacyIDEA Authenticator app. The latest version includes simplified push token configurations, improved stability and a new user interface.
NetKnights host second internal unconference

In the middle of the Harz mountains, the NetKnights set up camp to discuss organizational and technical topics.
Multi-Factor-Authentication at the Windows desktop – also on the road

As of today the privacyIDEA Credential Provider is available in version 3.2. The offline functionality in regards to multiple users and multiple tokens was improved.
Multi-Factor-Authentication privacyIDEA version 3.7 released
IT security company NetKnights releases version 3.7 of its professional
multi-factor authentication software privacyIDEA.
This provides reliable offline logon to Windows notebooks.
In addition, the administrator can now ensure that users do not forget
to scan the QR code with their smartphone when self-enrolling an OTP token.
As of today the new version is available via the Python Package Index and
in the community repositories for Ubuntu 16.04, 18.04 and 20.04.
