The OATH initiative is a collaboration of several companies from the authentication market. They aim to standardize authentication, algorithms, protocols and input and data formats.
The effort of standardization lead to several RFCs, which describe algorithms for the calculation of one time passwords. RFC4226 describes the event based HOTP, RFC6238 the time based TOTP and RFC6287 the flexible challenge response algorithm OCRA. (There is a blog post on this that contrasts HOTP and TOTP.)
Also important is RFC6030, that describes the transport and import format of the seed files for the tokens. Thus, if every vendor would provide the RFC6030 compatible seed file, you could import each OATH certified token data into every OATH certified authentication backend.
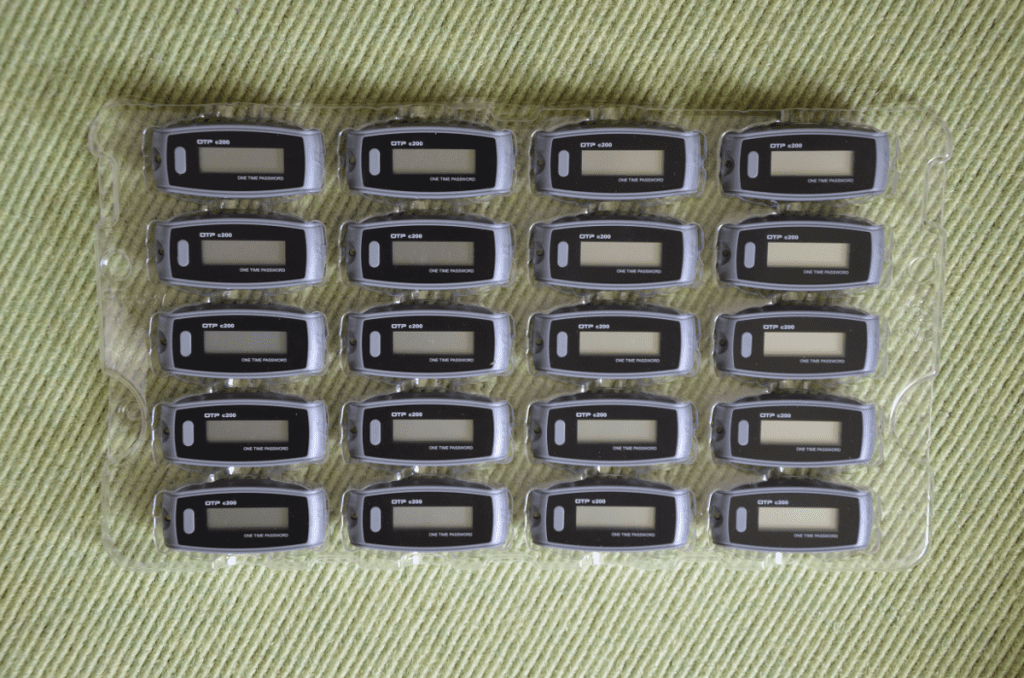
These well documented standards also pushed the propagation of one time passwords. Now it was easy for many vendors – also from far east – to build mathematically reliable and cryptographically secure authentication devices.
The same algorithms are used in smartphone apps, which are supposed to turn the smartphone into the second factor for authentication. The most known might be the Google Authenticator, which was attractive for already some years, due to its smooth rollout using a QR code for initialization.
But we need to point out, that the secret seed in the app on the smartphone is hard to protect from being copied or stolen – harder that on a not connected single purpose hardware device.
Nevertheless we use different smartphone apps as authentication device for our customer projects. Many customers love the rapid enrollment, the easy handling and the low costs. Often a mixed scenario with hardware token and smartphone apps is used. The backend of choice to handle mixed token scenarios is privacyIDEA.