privacyIDEA 2.15 on Univention Corporate Server
[av_textblock size=” font_color=” color=”] As of last week privacyIDEA 2.15 is now available on the Univention Corporate Server. This way enterprise customers which use the flexible multi factor authentication system privacyIDEA based on UCS now get support for the authentication device Nitrokey and more flexible RADIUS integration with firewalls and VPNs. The update of privacyIDEA can be […]
privacyIDEA Enrollment Station for Yubikey and Nitrokey
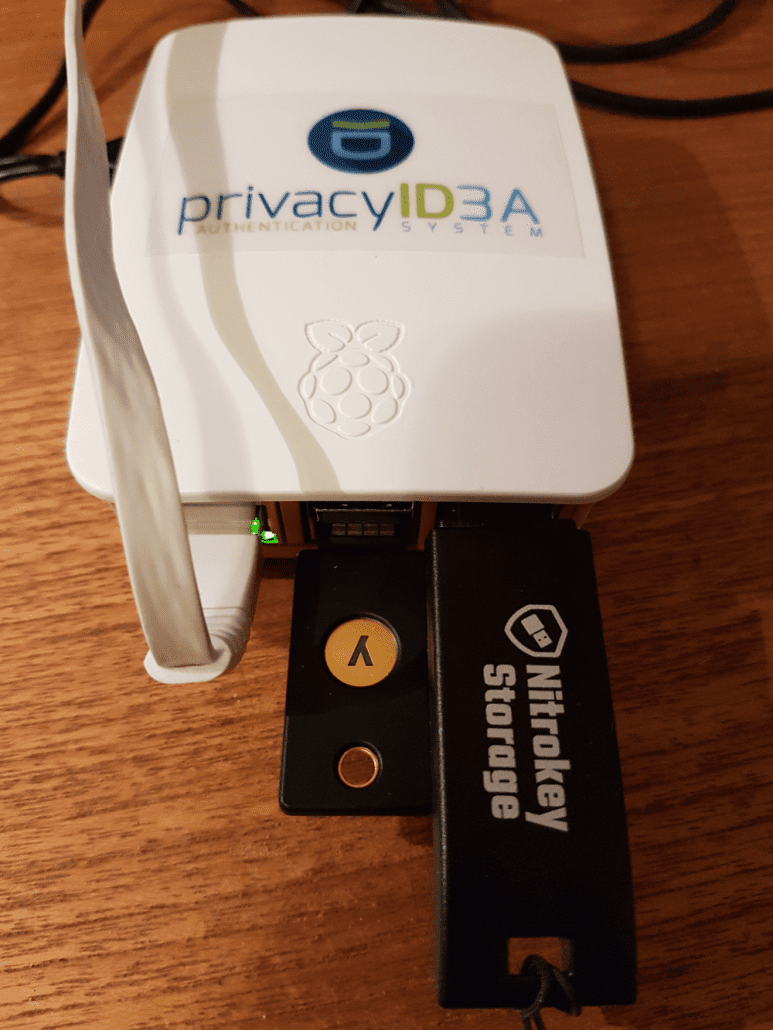
Using the Yubikey and the Nitrokey with privacyIDEA is great. With the privacyIDEA admin client you can initialize the secret seeeds on both devices and thus achieving the highest trust with privacyIDEA. The vendor does not generate the seeds anymore – you do. But to initializes these devices you need some drivers on your system. This […]
